Microsoft recently held a closed security bounty challenge for Azure Sphere, an application platform for internet-connected devices. While we did not participate in the three-month challenge which closed in August 2020, we were curious about the Azure Sphere devices which were designed with the “seven properties of highly secured devices” in mind.
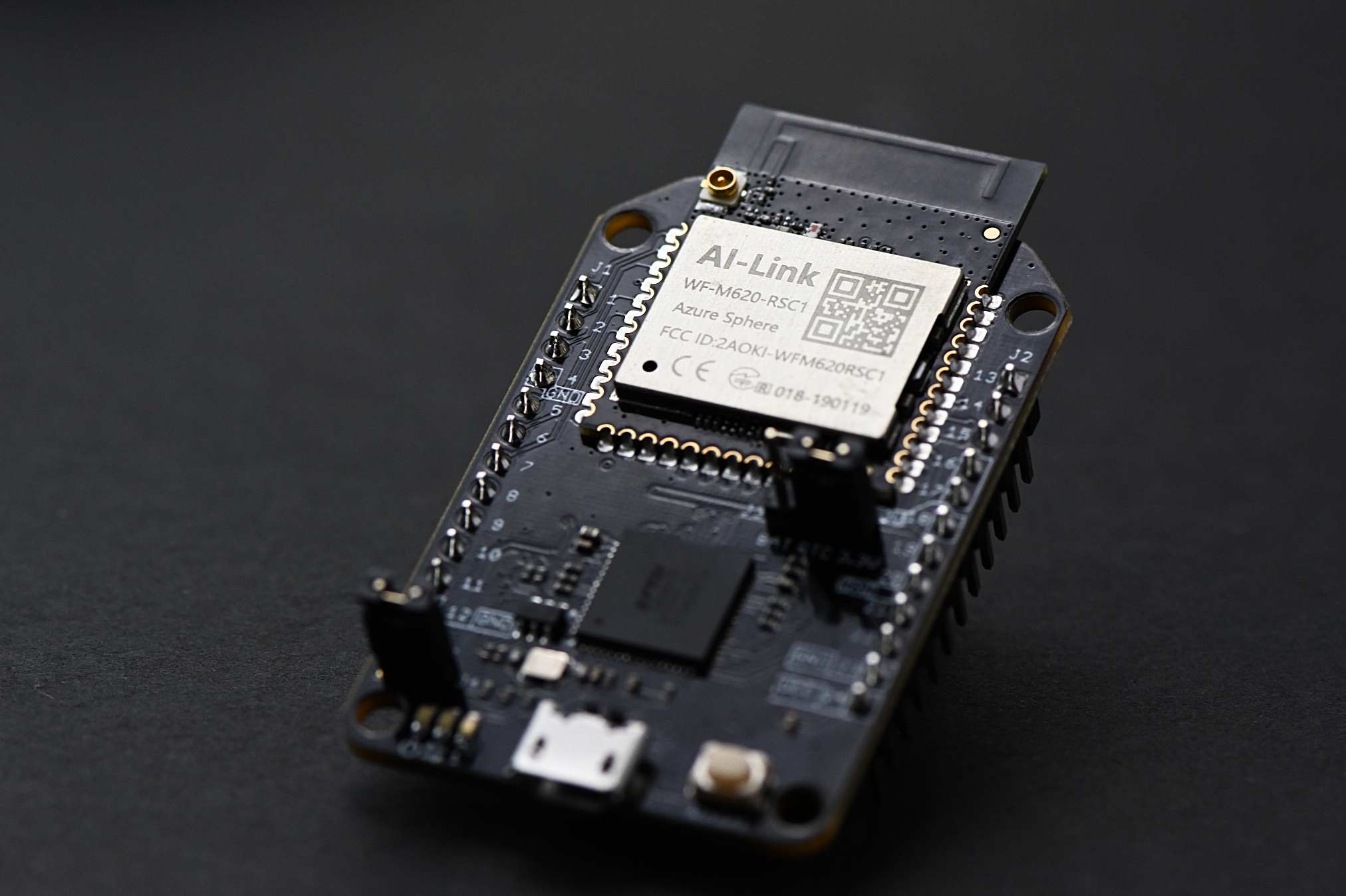
Since the development boards are cheap, we bought a few and took them apart. We tested Seeed MT3620 Mini Dev Boards running MS Azure Sphere OS 20.05.
Microsoft provides decent documentation for the APIs they are exposing and encouraging developers to use, but provides almost no information about the underling Linux operating system. Our reverse engineering and exploration of the board mostly focused on the Linux layer. We bundled together our notes and the tools we developed into a GitHub repository.
We developed several tools to help with the exploration and identified a couple issues. The issues that we found were also found by teams participating in the closed bounty challenge.
Our reverse engineering was with MS Azure Sphere OS 20.05. Currently the latest released version is 20.08 Update 1. Therefore, some of our reverse engineering notes may be out of date. The issues we and others found have been fixed in the latest release.
Issues
During our reverse engineering we identified three potential issues with MS Azure Sphere device.
- ASXipFS Device Nodes - It was possible to create app images with device nodes to allow an app to access devices it otherwise could not access.
- Peripheral Disable DoS - A malicious app on the device can disable peripherals used by other apps.
- Image Metadata Parsing DoS - Our image metadata parsing fuzzer can reliably cause the device to become non-bootable and require a recovery action.
Reverse Engineering Notes
We compiled our notes together in the form of a GitHub Wiki, available here.
Tools
Our tools include:
- Anvil Azure Sphere Test App - Spawns a busybox shell for system exploration and includes a few other testing commands.
- Toolchain/Libc - A compiled musl libc and gcc toolchain for the Azure Sphere devices. Mainly useful for a more complete set of headers.
- Package Tools - A set of Python scripts to parse image metadata, sign images with a developer certificate, and upload images.
- ASXipFS Unpacker - A modified cramfs-tools project to extract the files from an ASXipFS file system.
- Recovery Entry - A simple Python script to put the device into recovery mode.
- Fuzzers - Some fuzzers to test image metadata parsing and HTTP parsing.
Additional Projects
A number of companies and groups have also published their findings and notes on the MS Azure Sphere device:
About the Author
Michael Milvich is a Fellow at Anvil Secure. Prior to joining Anvil, Michael worked as a Senior Principal Consultant IOActive Inc, and as a Cyber Security Researcher at Idaho National Laboratory (INL). Michael got his start in embedded security hacking SCADA and ICS systems and later broadened to encompass a wide variety of embedded systems across many industries. Michael’s strong technical background combined with his years of general consulting have been utilized to assist some of the leading technologies and most advanced security groups in improving their security posture.